- HCL 68.3%
- Smarty 31.7%
* Allow private DNS Vnet link autoregistration * VM domain suffix support for private DNS zones * open Vault ports in firewalld * Update example folder: variables, README, etc Co-authored-by: Copilot <175728472+Copilot@users.noreply.github.com> |
||
|---|---|---|
| .github | ||
| docs | ||
| examples/default | ||
| templates | ||
| .copywrite.hcl | ||
| .env.local.example | ||
| .gitignore | ||
| .terraform-docs.yml | ||
| compute.tf | ||
| data.tf | ||
| dns.tf | ||
| iam.tf | ||
| image_data.tf | ||
| LICENSE | ||
| load_balancer.tf | ||
| locals.tf | ||
| outputs.tf | ||
| README.md | ||
| resource_group.tf | ||
| Taskfile.yml | ||
| terraform.tf | ||
| variables.tf | ||
Vault Enterprise HVD on Azure VM
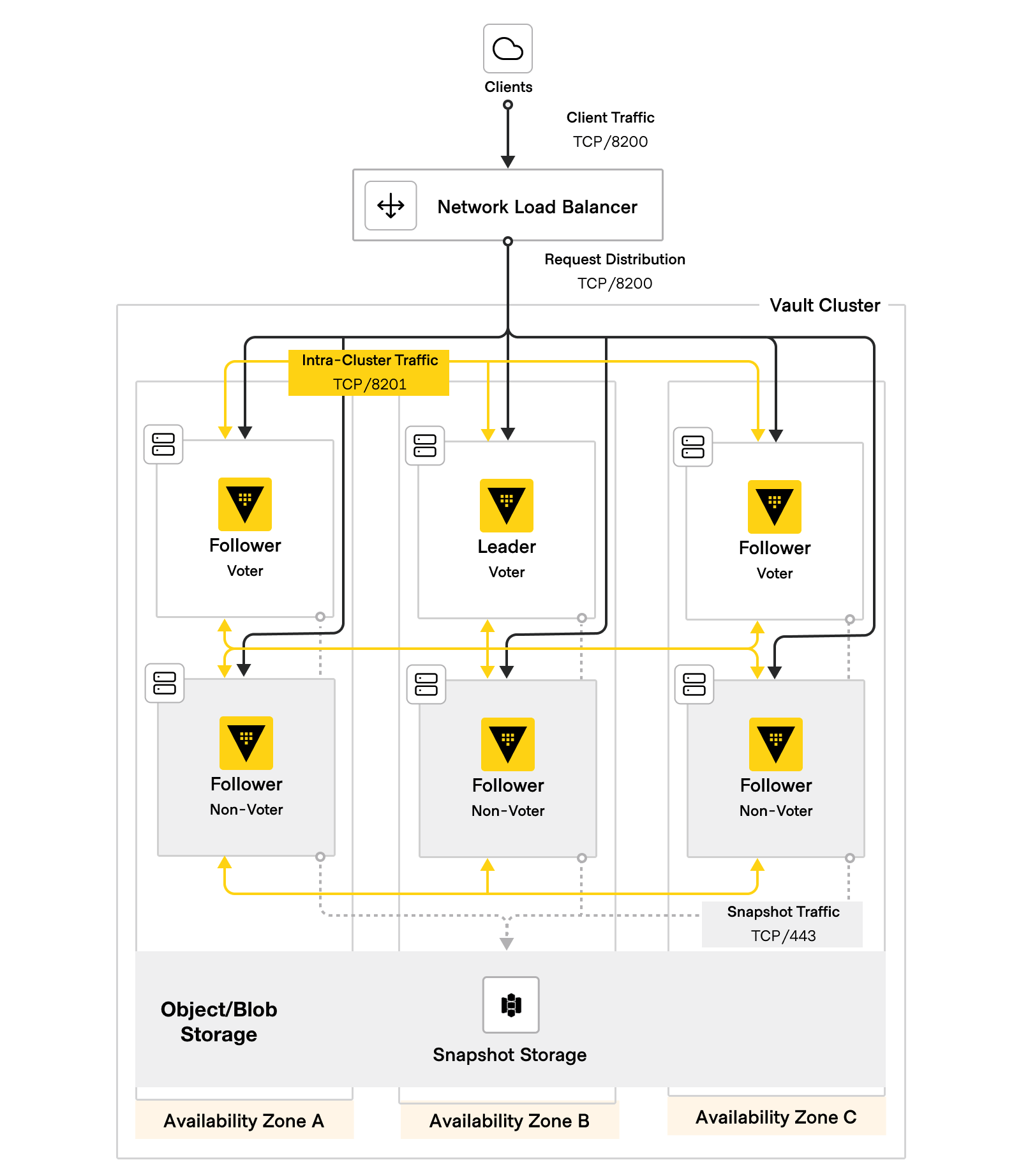
Terraform module aligned with HashiCorp Validated Designs (HVD) to deploy Vault Enterprise on Azure using Virtual Machines. This module deploys Vault Enterprise with integrated storage.
Prerequisites
This module requires the following to already be in place in Azure:
- An Azure Subscription with the following:
- Virtual Network
- NAT gateway
- Azure Key Vault containing:
- A cryptographic key for auto-unseal
- The necessary secrets to deploy Vault such as the license and TLS certificates (note variables ending in
_keyvault_secret_id)
Deployment
Upon first deployment, Vault servers will auto-join and form a fresh cluster. The cluster will be in an uninitialized, sealed state. An operator must then connect to the cluster to initialize Vault. When auto-unseal is used via Azure Key Vault, the Vault nodes will automatically unseal upon initialization.
Examples
Example deployment scenarios can be found in the examples directory of this repo here. These examples cover multiple capabilities of the module and are meant to serve as a starting point for operators.
Deployment Options
TLS
There is a helper doc for tls cert generation should you need it TLS.
Load Balancing
This module supports the deployment of Azure's TCP Layer 4 load balancer to sit in front of the Vault cluster. The load balancer can be external (public IP) or internal (private IP) and is configured to use Vault's sys/health API endpoint to determine health status of Vault to ensure clients are always directed to a healthy instance when possible.
The variable lb_is_internal is used to dictate if the load balancer should be exposed publicly. The default is false.
Key Vault
This module requires auto-unseal and defaults to the Azure Key Vault seal mechanism. As a prequisite to deployment, the module requires both the Azure Key Vault and Key Vault Key to be provisioned (see vault_seal_azurekeyvault_vault_name and vault_seal_azurekeyvault_unseal_key_name variables below).
Terraform configuration
Requirements
| Name | Version |
|---|---|
| terraform | >= 1.9 |
| azurerm | >= 3.0 |
Providers
| Name | Version |
|---|---|
| azurerm | >= 3.0 |
Resources
Inputs
| Name | Description | Type | Default | Required |
|---|---|---|---|---|
| friendly_name_prefix | Friendly name prefix for uniquely naming Azure resources. | string |
n/a | yes |
| location | Azure region for this Vault deployment. | string |
n/a | yes |
| prereqs_keyvault_name | Name of the existing 'prereqs' Key Vault to use for prereqs Vault deployment, containing secrets for Vault license and TLS certs. | string |
n/a | yes |
| prereqs_keyvault_rg_name | Name of the Resource Group where the 'prereqs' Key Vault resides. | string |
n/a | yes |
| vault_fqdn | Fully qualified domain name of the Vault cluster. This name must match a SAN entry in the TLS server certificate. | string |
n/a | yes |
| vault_license_keyvault_secret_id | ID of Key Vault secret containing Vault license. | string |
n/a | yes |
| vault_seal_azurekeyvault_unseal_key_name | Name of the existing Azure Key Vault key contained in var.vault_seal_azurekeyvault_vault_name to use for auto-unseal |
string |
n/a | yes |
| vault_seal_azurekeyvault_vault_name | Name of the existing Azure Key Vault vault holding Vault's unseal key. Can be the same as var.prereqs_keyvault_name. |
string |
n/a | yes |
| vault_subnet_id | Subnet ID for Vault server VMs. | string |
n/a | yes |
| vault_tls_ca_bundle_keyvault_secret_id | ID of Key Vault secret containing Vault TLS custom CA bundle. | string |
n/a | yes |
| vault_tls_cert_keyvault_secret_id | ID of Key Vault secret containing Vault TLS certificate. | string |
n/a | yes |
| vault_tls_privkey_keyvault_secret_id | ID of Key Vault secret containing Vault TLS private key. | string |
n/a | yes |
| vnet_id | VNet ID where Vault resources will reside. | string |
n/a | yes |
| additional_package_names | List of additional repository package names to install | set(string) |
[] |
no |
| availability_zones | List of Azure Availability Zones to spread Vault resources across. | set(string) |
[ |
no |
| common_tags | Map of common tags for taggable Azure resources. | map(string) |
{} |
no |
| create_lb | Boolean to create an Azure Load Balancer for Vault. | bool |
true |
no |
| create_private_dns_zone_vnet_link | Boolean to create a virtual network link between the private DNS zone and the VNet. Only valid when create_vault_private_dns_record is true. |
bool |
true |
no |
| create_private_dns_zone_vnet_link_autoregistration | Boolean to enable autoregistration on virtual network link between the private DNS zone and the VNet. | bool |
false |
no |
| create_resource_group | Boolean to create a new Resource Group for this Vault deployment. | bool |
true |
no |
| create_vault_private_dns_record | Boolean to create a DNS record for Vault in a private Azure DNS zone. private_dns_zone_name must also be provided when true. |
bool |
false |
no |
| create_vault_public_dns_record | Boolean to create a DNS record for Vault in a public Azure DNS zone. public_dns_zone_name must also be provided when true. |
bool |
false |
no |
| custom_startup_script_template | Name of custom startup script template file. File must exist within a directory named ./templates within your current working directory. |
string |
null |
no |
| is_govcloud_region | Boolean indicating whether this Vault deployment is in an Azure Government Cloud region. | bool |
false |
no |
| key_vault_cidr_allow_list | List of CIDR blocks to allow access to the Key Vault. | list(string) |
[] |
no |
| lb_is_internal | Boolean to create an internal or external Azure Load Balancer for Vault. | bool |
false |
no |
| lb_private_ip | Private IP address for internal Azure Load Balancer. Only valid when lb_is_internal is true. If not provided, a dynamic private IP will be assigned from the lb_subnet_id subnet. |
string |
null |
no |
| lb_subnet_id | Subnet ID for Azure load balancer. | string |
null |
no |
| private_dns_zone_name | Name of existing private Azure DNS zone to create DNS record in. Required when create_vault_private_dns_record is true. |
string |
null |
no |
| private_dns_zone_rg | Name of Resource Group where private_dns_zone_name resides. Required when create_vault_private_dns_record is true. |
string |
null |
no |
| public_dns_zone_name | Name of existing public Azure DNS zone to create DNS record in. Required when create_vault_public_dns_record is true. |
string |
null |
no |
| public_dns_zone_rg | Name of Resource Group where public_dns_zone_name resides. Required when create_vault_public_dns_record is true. |
string |
null |
no |
| resource_group_name | Name of Resource Group to use for Vault cluster resources | string |
"vault-ent-rg" |
no |
| systemd_dir | Path to systemd directory for unit files | string |
"/lib/systemd/system" |
no |
| vault_default_lease_ttl_duration | The default lease TTL expressed as a time duration in hours, minutes and/or seconds (e.g. 4h30m10s) |
string |
"1h" |
no |
| vault_dir_bin | Path to install Vault Enterprise binary | string |
"/usr/bin" |
no |
| vault_dir_config | Path to install Vault Enterprise binary | string |
"/etc/vault.d" |
no |
| vault_dir_home | Path to hold data, plugins and license directories | string |
"/opt/vault" |
no |
| vault_dir_logs | Path to hold Vault file audit device logs | string |
"/var/log/vault" |
no |
| vault_disable_mlock | Boolean to disable mlock. Mlock should be disabled when using Raft integrated storage. | bool |
true |
no |
| vault_enable_ui | Boolean to enable Vault's web UI | bool |
true |
no |
| vault_group_name | Name of group to own Vault files and processes | string |
"vault" |
no |
| vault_max_lease_ttl_duration | The max lease TTL expressed as a time duration in hours, minutes and/or seconds (e.g. 4h30m10s) |
string |
"768h" |
no |
| vault_plugin_urls | (optional list) List of Vault plugin fully qualified URLs (example ["https://releases.hashicorp.com/terraform-provider-oraclepaas/1.5.3/terraform-provider-oraclepaas_1.5.3_linux_amd64.zip"] for deployment to Vault plugins directory) | list(string) |
[] |
no |
| vault_port_api | TCP port for Vault API listener | number |
8200 |
no |
| vault_port_cluster | TCP port for Vault cluster address | number |
8201 |
no |
| vault_raft_performance_multiplier | Raft performance multiplier value. Defaults to 5, which is the default Vault value. | number |
5 |
no |
| vault_seal_type | n/a | string |
"azurekeyvault" |
no |
| vault_telemetry_config | Enable telemetry for Vault | map(string) |
null |
no |
| vault_tls_disable_client_certs | Disable Vault UI prompt for client certificates | bool |
false |
no |
| vault_tls_require_and_verify_client_cert | Require and verify client certs on API requests | bool |
false |
no |
| vault_user_name | Name of system user to own Vault files and processes | string |
"vault" |
no |
| vault_version | Version of Vault to install. | string |
"1.17.3+ent" |
no |
| vm_admin_username | Admin username for VMs in VMSS. | string |
"ubuntu" |
no |
| vm_boot_disk_size | The disk size (GB) to use to create the boot disk | number |
64 |
no |
| vm_custom_image_name | Name of custom VM image to use for VMSS. If not using a custom image, leave this blank. | string |
null |
no |
| vm_custom_image_rg_name | Name of Resource Group where vm_custom_image_name image resides. Only valid if vm_custom_image_name is not null. |
string |
null |
no |
| vm_disk_encryption_set_name | Name of the Disk Encryption Set to use for VMSS. | string |
null |
no |
| vm_disk_encryption_set_rg | Name of the Resource Group where the Disk Encryption Set to use for VMSS exists. | string |
null |
no |
| vm_domain_suffix | Domain suffix to append to VM hostnames. If not provided, VMs will use default Azure domain. This is required for cross-VNET hostname resolution for replication. | string |
null |
no |
| vm_enable_boot_diagnostics | Boolean to enable boot diagnostics for VMSS. | bool |
false |
no |
| vm_os_image | The OS image to use for the VM. Options are: redhat8, redhat9, ubuntu2204, ubuntu2404. | string |
"ubuntu2404" |
no |
| vm_sku | SKU for VM size for the VMSS. | string |
"Standard_D2s_v5" |
no |
| vm_ssh_public_key | SSH public key for VMs in VMSS. | string |
null |
no |
| vm_vault_data_disk_size | The disk size (GB) to use to create the Vault data disk | number |
200 |
no |
| vmss_vm_count | Number of VM instances in the VMSS. | number |
6 |
no |
| worker_msi_id | value of the worker MSI id | string |
null |
no |
Outputs
| Name | Description |
|---|---|
| load_balancer_ip | IP address of load balancer's frontend configuration |
| resource_group_name | Name of the Resource Group. |
| vault_cli_config | Environment variables to configure the Vault CLI |
| vault_server_private_ips | The Private IPs of the Vault servers that are spun up by VMSS |